This is what Identity and Access Management does!
Get an overview of the cidaas features.

Single Sign On
Uniform login and stay logged in
Users can log in to all services using a single identity. And after a one-time login, they can access all content and services in different portals without having to log in again.
If the user changes to another service, then the access is checked by the cidaas SSO login. In case of a successful request, he gets access to these resources. The single sign-on session can be easily configured whether session time or automatic logout after inactivity.
Consent management
Obtaining and managing consents
With the cidaas Consent Management feature, companies can now give their customers full control over their personal data.
cidaas enables users – in compliance with EU GDPR – to view and edit consent preferences, or to revoke or confirm the consent given. This restricts the use and possible misuse of your data by third parties.
Companies ensure transparency in data management and effectively communicate changes to data protection guidelines and general terms and conditions to their customers, which are recorded in an audit trail.
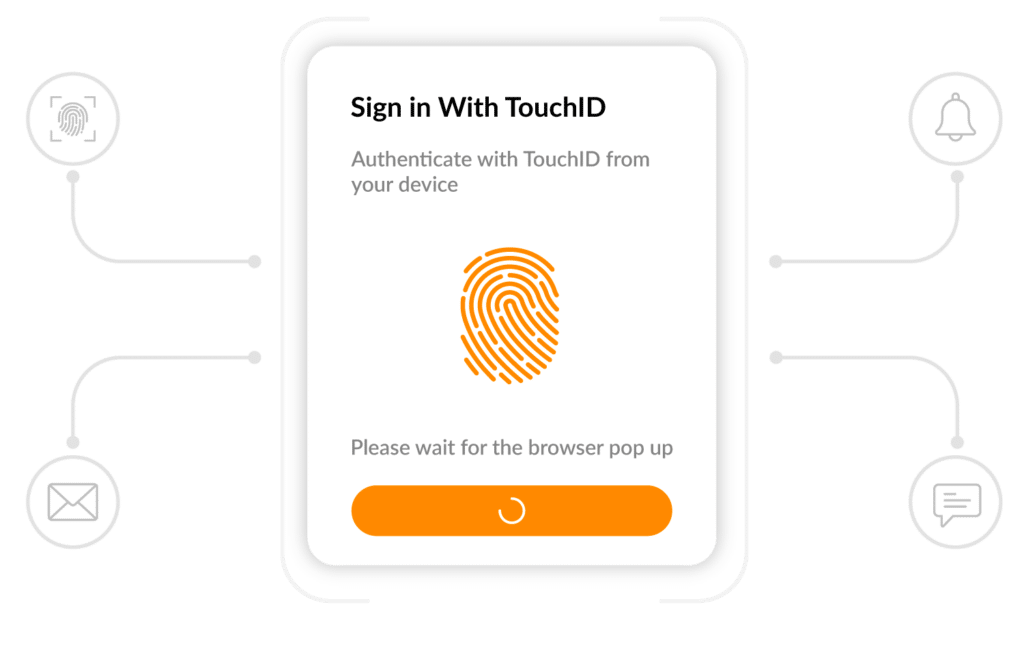
Passwordless authentication
Bye bye password! The future of the login
With passwordless authentication from cidaas, passwords become obsolete and customer login much more convenient. Whether biometric methods such as TouchID/FaceID, the FIDO2 standard or via a one-time password (OTP) to the registered email, mobile phone number or the Authenticator App – the login is secure, fast and inspires users.
Passwordless authentication not only ensures a great user experience, but also increases security, because the risk factor of a bad or stolen password is eliminated.
Multi-factor authentication
High security with a second factor
Additional security with cidaas multi-factor authentication. Configure multi-factor authentication flexibly to your requirements. Whether mandatory for some applications or as an option for all users.
Also increase security with cidaas Smart Multi-Factor Authentication and secure the login in case of suspicious behavior or unauthorized access with a Second Factor (2FA).
cidaas offers a variety of authentication options, from one-time codes via email/SMS/IVR to authenticator apps and push messages to a wide range of biometric authentication methods.
Fraud detection and cybersecurity
From bot attack to suspicious behavior
To verify customers and identify fraudsters, cidaas uses de-duplication, strong forecasting factors and big data analyzes. And stop fraudulent attempts or suspected cases with built-in tools.
In case of suspicious activity, according to your preferences, both you and your users can be alerted, and login attempts and IP address can be blocked.
API Security
Securing APIs with OAuth2
APIs are a basic building block of modern software architectures. With API security from cidaas and the OAuth2 standard, securing APIs is simple and transparent. The authorization on the APIs is done via OAuth2 tokens that authorize users or applications to use the API.
Using the reporting and monitoring in cidaas, profiling for marketing or fraud detection is easy – because it is clear which applications and which users are using which APIs.
Group Management
For family, friends or business
The cidaas group management enables to group any user and to delegate the administration of the group. In this way, the different areas or teams in a company can be easily structured and the administration of the group can be delegated to the team or area manager.
The cidaas group management is very flexible, so new groups can be created, edited or removed quickly to easily reflect the dynamics of today’s working world. But the use cases for the cidaas group management are manifold, e.g. the mapping of the family as a group with the parents as group admin for a streaming service is perfect or a group of friends visiting a stadium together.
The group management not only allows a professional grouping of users, but also creates added value for the users through self-administration with a perfect user experience and a reduction in costs on the company side.
De-duplication & Identity Linking
User duplicate detection and linking
Our big data analysis tools learn from the user profiles and recognize duplicate user profiles, even during registration. Only a single identity of the user is saved.
Social Login
Easy and fast registration with social login
Users can easily register using their preferred social network account.
The cidaas social media registration feature allows the end-user to register for a cidaas identity using his trusted social media account. This means much more comfort for the users: not having to create one more userId / password combination, the registration is automatically filled out and even the confirmation by e-mail is no longer necessary.
User management and user profiles
Individual user attributes and user self services
Registered users can manage their own account in a dedicated / specially designed cidaas user page.
This allows you to reset passwords, to change passwords, to set up 2-FA settings and to edit your own address if necessary. To a certain extent more can be changed in the corresponding database entry.
Progressive Profiling
Extend user information based on context
Lengthy registration processes are a thing of the past and put users off. With Progressive Profiling from cidaas, it is possible to record and expand user data contextually. For example, the delivery address no longer has to be entered when registering but when ordering, or the mobile phone number when ordering from the delivery service.
With Progressive Profiling a smooth customer journey is created where the user profile can be completed easily and bit by bit – without disturbing the user and also easily understandable due to the benefit and the context. It enables the user to be guided from the prospect to the customer.
Device management
Management of devices of an identity
Discover not only the user but their devices as well. In the age of the Internet of Things and a rapidly increasing number of networked devices, your customer uses many devices, even simultaneously.
cidaas recognizes these devices and informs you about them. The perfect accelerator for your digital transformation.
Real World Identification
Linking digital and real identities
By linking real and digital identities, you can now improve personalized customer interactions and leverage all potential business opportunities. cidaas helps companies to send business-related messages, advertising content and notifications to registered customers when they enter the defined surveillance areas around the business facilities, based on signals received from installed beacons and cameras.
This feature facilitates customer engagement and can also be used to manage employee communications and employee access to the premises.
cidaas ID Validator
Digital identity verification using AI
The cidaas ID validator offers AutoIdent procedures for an innovative service for the verification of ID cards, passports and driving licences. The user is guided through a simple and automated process of recording video sequences of himself and the ID.
The ID validator carries out various checks, including facial recognition, liveness detection, as well as checking the features of the ID, e.g. holograms. In doing so, it relies on modern AI technologies to enable fast and automated processing.
For ID and passport verification, the cidaas ID validator complies with the highest European standards for digital identification.

What customers say about cidaas
Philipp Hanraths
Manager IT E-Commerce & IT Architecture, Takko Holding GmbH
“We chose cidaas because the flexible CIAM system allows us to easily migrate to an advanced, digitalized world. For example, we can integrate existing user accounts into customer identity management via an individual connector. Via cidaas, our private and business customers can stay in touch with us anytime and anywhere – regardless of the channel, device, or app and integrates all new services. With cidaas, we have found the right solution for us.”
Tobias Baumgart
Director eCommerce Platform, Conrad Electronic SE
“In times of mobile devices, decentralized systems, and the cloud, the topic of identity management is becoming increasingly important in the digital space. cidaas represents the ideal IDaaS solution for us to drive the digital transformation in our corporate structure. cidaas not only provides us with increased operational efficiency but also improves the usability of our channels. We are very happy to have found a strong partner in identity and access management with cidaas.”
Dirk Semmler
Head of IT, LORCH Schweißtechnik GmbH
“Before we decided on cidaas, we had already tested several identity management systems and had already worked with another provider for several years. However, none of the other systems could fulfill all our requirements “out-of-the-box”. With cidaas we have now found the optimal software suite for us, which, thanks to state-of-the-art technology, has completely implemented our requirements in only 3 months of project time. cidaas delivers what it promises and is fast, secure, and unrivaled Swabian.”
Alexander Mietzke
Head of Digital Technologies, REHAU AG + Co
“cidaas is a full-fledged CIAM SaaS solution from WidasID GmbH and is developed and hosted in Germany. The solution is easy to integrate into common SaaS applications and contains many standard functions but also innovative features such as the integration of IoT devices and integrated consent management. cidaas is based on a microservices architecture and thus enables flexible and dynamic scaling and is subject to constant service improvements.”
John Tolbert
KuppingerCole Analysts
“Modern software is intelligent, innovative and easy to use. With the self-developed product cidaas – Customer Identity Management as a Service – Widas ID GmbH has created exactly such a solution. We at CAMLOG use cidaas for central user and identity management for our shops and portals – so our customers also benefit from the user-friendly service.”
Karlheinz Klein
Head of e-Business, Camlog Management GmbH
“Digitization in the insurance industry has accelerated extremely and we are experiencing strong growth in the number of users on our digital services. Introducing cidaas now was the right decision for us at the right time so that we can get started straight away with our next ideas and innovations.”
Stephanie Kern
Business Development der die Bayerische IT GmbH
1B+
Active Users
50K+
Passwordless authentications / week
300+
Customers
182+
Countries
Every feature counts.
It´s the synergy that makes the difference.
Discover how cidaas combines security, convenience, and scalability in a single solution.
