Bye password, hello modern login! – IT Afterwork
Just a quick glance into the glass-sphere is enough to see that the advancing digitalization demands an alternative to confirm our identities. Since several years now, the digital age has been opening new, more convenient ways for society to communicate, network and present itself. Companies are confronted with the challenge of making the volume of data tangible and offering their customers an extraordinarily convenient, digital and secure experience. This also includes the important process of checking digital identities against real identities to ensure security. In short, authentication.
The user experience should be as convenient as possible across the industry, as it is today’s society that most craves agility and time savings, both at home and at work. With the majority of everyday processes already running entirely digitally, there is almost no way around an authentication process. But which processes create a perfect balance between security and convenience?
The password – liked and disliked
The lecture was preceded by a fascinating live survey of the audience.

Would you have known the answer? Because 42% of the audience was wrong. Behind the cryptic combination ji32k7au4a83 is a system for transliterating Mandarin and means “My Password”. This password has been proven to be much more vulnerable to cyber attacks than Katzenfan75. In addition to great surprise, the thought slowly began to spread that passwords might not be as secure as they appear to be, especially as we move internationally in the digital world.
Passwords are not insecure per se, but thanks to today’s technology, they can be quickly picked up and circumvented. Through phishing, criminals deceive users; through real-looking sites, they deceive users. They willingly enter their password on the pages that appear trustworthy. The complexity of the password therefore does not play an important role at all. Complexity also plays a subordinate role in password spraying, as the system searches for the correct combination of characters until it recognizes it. This is easy with today’s computing power.
The so-called Credential Stuffing makes excellent use of the factor of multiple passwords. If a password has already been stolen from other data sources, it is automatically tried out on thousands of portals to gain illegal access without having to steal new passwords. The so-called Credential Stuffing makes excellent use of the factor of multiple passwords. If a password has already been stolen from other data sources, it is automatically tried out on thousands of portals to gain illegal access without stealing new passwords.
Whether we are users, companies or employees, we are forced to protect our data or let it be protected sufficiently. The question of safe and at the same time convenient solutions for this is becoming more and more important. But which options will prevail as established standards in the future?
Modern authentication – balance between convenience and security
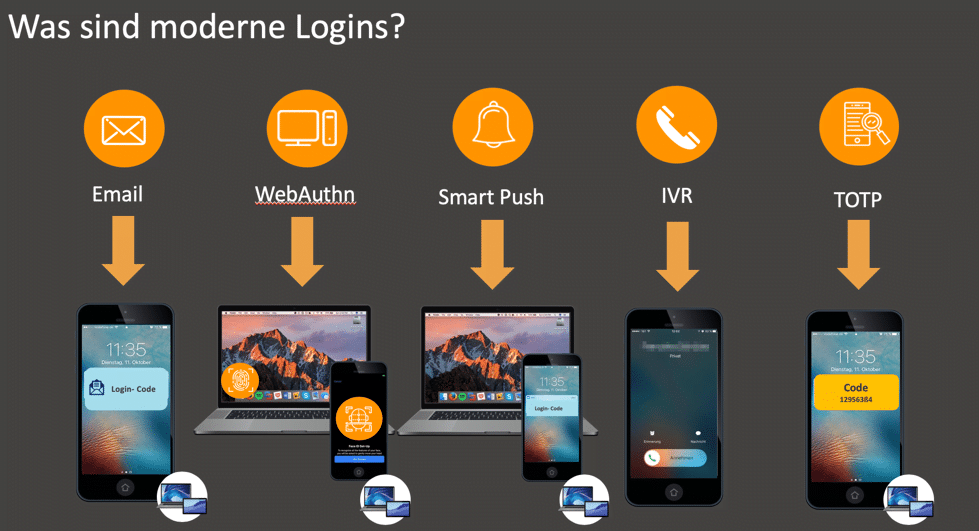
Already familiar solutions such as passwords, pins and TAN lists are titled as insufficiently secure and impractical. As a result, modern authentication methods are becoming increasingly popular. These will be visualized below for your understanding.

Modern authentication – balance between convenience and security Modern authentication – balance between convenience and security If one observes the trend, it becomes clear that biometric solutions are gaining in popularity. Since almost everyone owns a hard device with this integrated technology, it is very easy for companies to integrate it into their access management and no further costs are incurred. In addition, major brands have already done preliminary work and created an initial awareness of the topic and have persuaded users to use mainly biometric access.
If you compare the time it takes to reset a password with the time it takes to authenticate by e-mail, it quickly becomes clear that the password has to be clearly superior to modern authentication methods in terms of time. According to a study, employees spend eleven hours a year resetting their passwords. If this time is offset against the average hourly wage, the damage per company is around five million dollars.3
So modern authentication methods provide not only more user comfort, higher security and significant cost savings, as well as increased work efficiency and employee motivation.
TOP 3 questions during the presentation
After the exciting lecture, there were obviously some open questions due to the relevance and depth of the topic. In the following TOP 3 questions, which attracted special attention.
Question: Can a fingerprint on a selfie (e.g. by a peace sign) be recognized, stolen and reconstructed?
Biometric procedures do not belong to a stealable knowledge. A password is usually recorded either in a password manager or in certain documents. This creates a security risk that biometric procedures do not have. It is potentially possible to find out biometric characteristics, but the effort to hack biometric authentication methods is much higher than with conventional alternatives such as passwords. Nowadays it is unimaginable that biometric identifiers can be stolen in a large scale because such a procedure requires a very high investment, which only becomes interesting for cybercriminals when it comes to stealing the identities for instance diplomats.
Question: How long does it take until biometric methods can be hacked as easily as conventional passwords?
It is a race between fraud detection, i.e. the protection of identities, and cybercriminal activity. Passwords must first be phased out completely so that cybercriminals can start researching and hacking biometrics. So far, there is no clear evidence that hackers have already reached the stage where they can efficiently trick modern authentication methods. In addition, the question of the location of the identification feature always arises. Where is it and how can I attack it? How expensive and inconvenient will it be to steal this digital identity?
Question: How far has standardization progressed in the field of modern authentication?

Standardisation initially harbours the advantage of efficient error and risk management due to the high number of uses. Such procedures are thus more stable, secure and agile in their functioning. A very established procedure is the WebOAuthn Standard (FIDO2), which provides a password-free experience in a specific browser. Standardizations like this, but also Open ID Connect and OAuth2.0, allow a feather-light integration into your own applications.
By the way, after the question and answer session there was networking time with a very nice buffet!
Conclusion
The IT Afterwork was another milestone for cidaas. The lively attention and the interested exchange in the afterwork showed that the topic of passwordless authentication is becoming more and more anchored in our minds and is gaining in importance. The new authentication methods are slowly gaining acceptance among companies. The entire cidaas team would like to thank the organizers DigitalHub Nordschwarzwald and innotec GmbH once again.
In the future, fulfilling the customer and user needs for a balance between security and comfort when logging in will become more and more important. Convenience is often put before the factor of security by the users. This phenomenon is not only visible in access management, but also in industries such as the automotive, real estate and service sectors. Here, convenience is the most important factor in a purchase decision. Every company, from small to large, should immediately start looking for suitable solutions to continue to compete in the digital age and to efficiently satisfy the needs of its customers.
How do you want to secure your access in the future?
cidaas. identity is everything.
[DISPLAY_ULTIMATE_SOCIAL_ICONS]
