The new data protection regulation turns 1 year old
The new edition of the European Union – General Data Protection Regulation (EU-GDPR) celebrates its first anniversary today.
But even one year after it’s coming into force, many still ask what exactly is behind the GDPR and the effects it has on companies and the management of personal data.
The Data Protection Act of the European Union, in effect since 25 May 2018, is considered one of the most important changes to data privacy regulations. It defines how the personal data of EU citizens must be handled. In short, citizens now have more rights to know their data, that companies store and can have the data deleted upon request. Businesses, on the other hand, must ensure that data is handled in a lawful manner and make the processing of personal data more transparent and secure. The regulation comes with clearly defined penalties for non-compliance – companies could be fined up to 4% of their annual global turnover or €20 Million (whichever is greater).
Less progress in compliance with the data protection regulation
One year after the GDPR came into effect, there was no major wave of warnings, but more than 59,000 violations were reported throughout Europe. A study by the Digital Association Bitkom e.V. also shows that so far only 24% of all German companies have fully implemented the GDPR. This leads to the conclusion that many companies still have difficulties in fully implementing and complying with the Data Protection Regulation.
[vc_row][vc_column][vc_column_text]
The successful implementation of the GDPR remains a major challenge.
The hurdles that companies still face today are more or less the same as they were a year ago:
- Numerous data silos: Companies often store personal customer data across multiple systems. This makes it very difficult to gain a holistic view of personal data and the corresponding processing of data.
- Incomplete Self-Services: The GDPR stipulates that the personal data of people should always be up to date – preferably by leveraging the function of self-service. Due to the data silos that companies have, this becomes an impractical challenge.
- Insufficient data governance: Access to data must be mapped in all applications via centralized data access policies. In most cases, these role-based access privileges, which should be built according to the “need to know” principle, are not comprehensively implemented across the operational file system.
- Lack of data security: The GDPR requires the implementation of technical and organisational measures (TOM) to protect data. Many companies have not yet fully complied with these security requirements, which include data encryption.
[/vc_column_text][vc_column_text]
Customer Identity and Access Management helps you become GDPR-compliant
For companies that have not yet completed their GDPR homework, the implementation of customer identity and access management software such as cidaas is the optimal solution for managing digital identities on a single unified platform.
CIAM makes you GDPR compliant at one go:
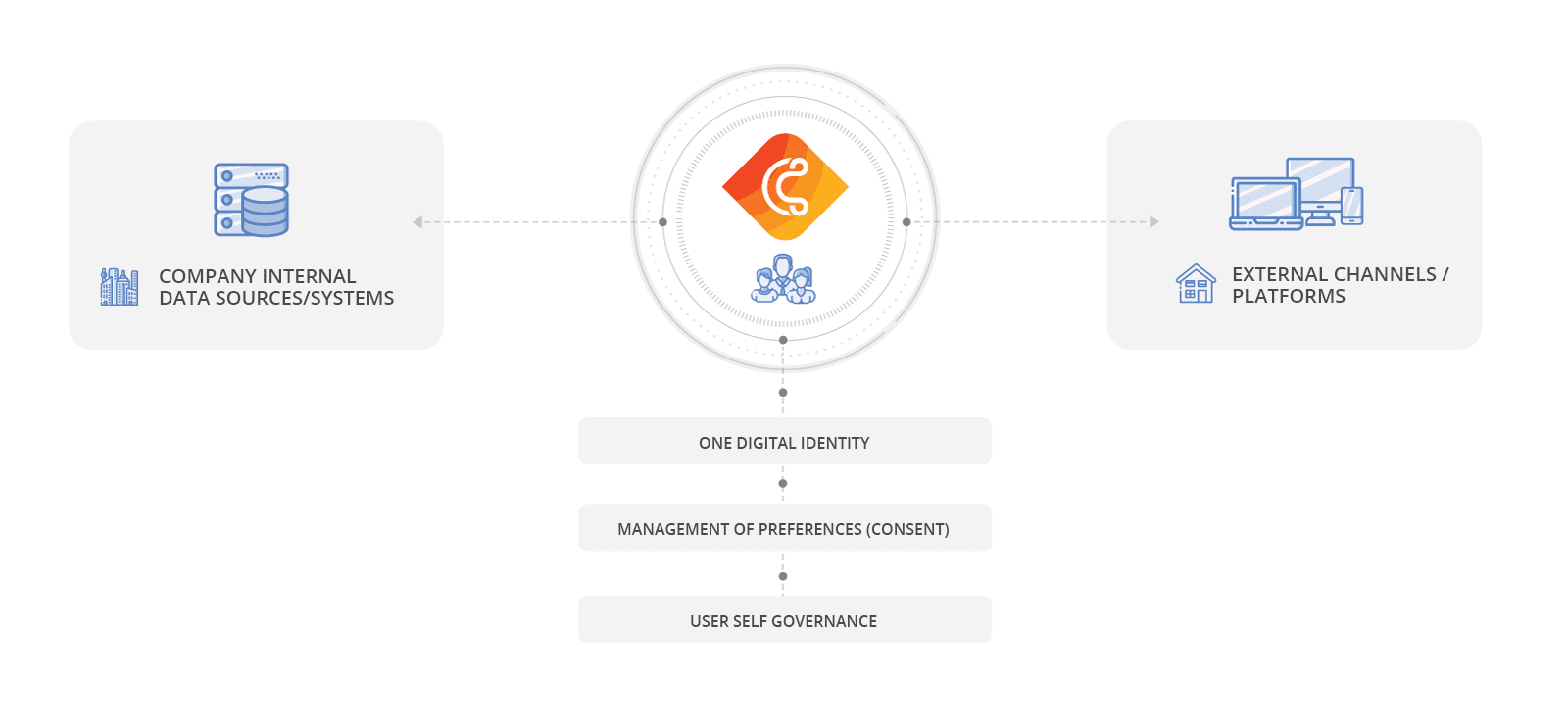
Figure 1: cidaas centralizes the management of your digital identities on one platform
- Management of consents
Informational self-determination of every single individual provides the basis of the GDPR. As soon as the data subject gives his unambiguous consent, or a legal allowance is granted the data processing is permitted (principle of prohibition).- Companies should collect the consent of the data subject at the start of data collection e.g. during the registration process or if a change of the purpose of use occurs (art. 6 (1) point (a) GDPR)
- The data subject can withdraw his or her consent. The withdrawal shall be as easy as giving consent (art. 7 (3) GDPR)
- The company must provide a proof of consent on request (formal requirement, mandatory record) (art. 7 para. 1 EU-GDPR)

cidaas fully supports you in the management of consent preferences and offers you the possibility to send stored personal data (PII= personally identifiable information) to your customers at the push of a button.
- User Self-Services
According to Art. 5 para. 1 d), personal data must be factually correct and, if necessary, up to date. Furthermore, all reasonable measures must be taken to ensure that personal data which are inaccurate with regard to the purposes of their processing are deleted or rectified without delay (“accuracy”).
So why not give the customer himself the control over it? After all, he knows best about his personal data.
With cidaas, you return control over data management to the user and
thus ensure that the data is up to date. - Data Security
Art. 32 of the GDPR requires the implementation of technical and organisational measures (TOM) to protect data. However, what this means exactly and what actions must be taken to ensure data security is not specified in more detail.
A CIAM solution such as cidaas guards personal data and protects it from unauthorized access through procedures such as two-factor authentication (2FA) and biometric registration procedures. Furthermore, the integrated role and group management of cidaas makes it possible to trace exactly who accessed which data and which changes were made. Thus every data entry, change and deletion can be traced, as required by Art. 5 para. 1 EU-GDPR.
- One identity across multiple channels
In order to comply with the stricter regulations of the Data Protection Regulation, companies must abandon stand-alone applications.
Customer Identity and Access Management consolidates the existing data silos and enables the management of all user data on one platform.
Data protection can only be achieved through targeted identity management.
In the past, data protection was a fringe issue, but today violations are penalized with heavy fines. As current studies show, the implementation of the GDPR still has gaps in many companies today.
By using a Customer Identity and Access Management solution, you can master the technical requirements of the Data Protection Regulation.
Have you still not completely fulfilled the requirements of the GDPR and still need support in its implementation? Contact us or start today with our free cidaas Freeplan
CIAM Guide: What need to be considered when choosing a Customer Identity and Access Management solution?
Find out in our guide which criteria you should consider when making your decision.
