The Future of Living: The Connected Home and the Importance of Authentication and Authorization
The relation between user and device in the Connected Home
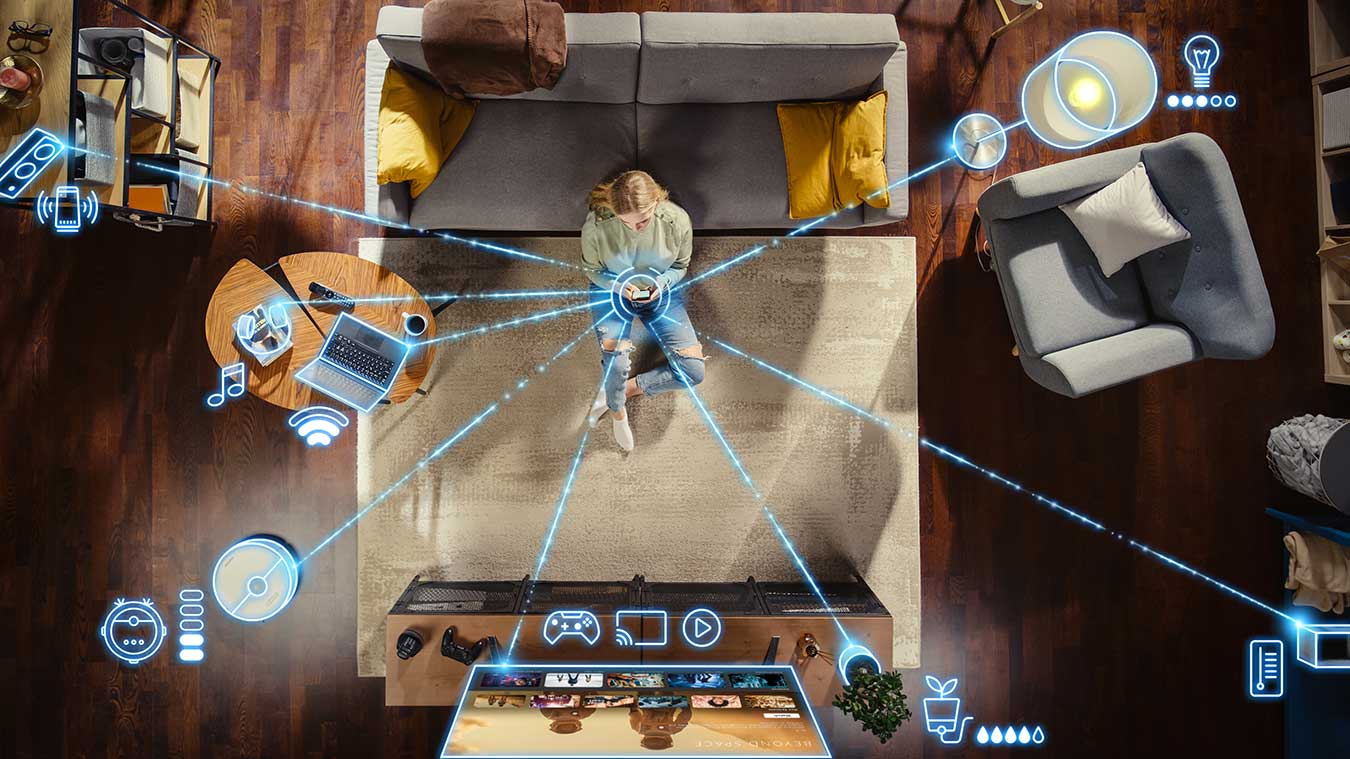
Connected Home is not just about devices communicating with each other, but also about the interaction between users and these smart devices. From smart thermostats, lighting systems and security cameras to voice-controlled assistants, these devices are designed to make life more convenient and efficient. They learn users’ preferences, adapt to their daily routines, and offer personalized experiences. The authentication and authorization of users to devices, of devices to each other, and the particularity that devices act on behalf of users, e.g., the smart refrigerator which automatically reorders products on behalf of the user, must be considered.
Authentication and Authorization in the Connected Home
The multitude of connected devices in the smart home makes end-to-end authentication and authorization essential. Authentication, for example, ensures that only authorized users can access devices and services, while authorization ensures that these users can only access the functions or data assigned to them.
This is where technology comes into play. From biometric identification methods such as fingerprint or facial recognition to one-time passwords (OTP) and security-related tokens, a wide variety of authentication methods can be used to verify user identity and prevent unauthorized access. It is important to select technologies that are both secure and user-friendly to ensure seamless interaction in the Connected Home.
Act on behalf of: When devices act on behalf of the user
An intriguing concept in the Connected Home is the ability of devices to act on behalf of the user. This feature, often referred to as “act on behalf of,” allows smart devices to make decisions and perform actions that are in the best interest of the user. A striking example is the networked refrigerator, which is equipped with sensors to monitor food inventory. It can automatically order new food when certain products run low. This brings a new dimension of convenience and efficiency to the smart home, as everyday tasks are automated, and the user has to worry less about details. However, this automation also poses challenges in terms of security and control. Implementing secure authentication and authorization mechanisms is critical to ensure that these smart devices are indeed acting in the user’s best interest and on the user’s behalf and cannot be manipulated by malicious actors. Here, a balance between automation and human control as well as transparency is of great importance to ensure both convenience and security in the Connected Home.
Security and privacy as a priority
While the smart home undoubtedly offers many advantages, security and data protection must not be neglected. Insecure connected devices could be potential gateways for hackers to steal personal information or use the device for malicious purposes. Therefore, manufacturers must adhere to strict security standards, provide regular updates and, in particular, implement authentication and authorization for users and devices.
cidaas: Leading Cloud Identity & Access Management in the Connected Home
cidaas has established itself as the leading cloud solution in the field of Identity & Access Management, also for the Connected Home. cidaas offers a comprehensive feature set to map authentication and authorization seamlessly and securely for networked devices and services.
With cidaas, manufacturers of connected devices can implement secure authentication that enables users to connect their smart devices easily and securely. Users can choose from a wide range of authentication methods, which enables convenient and at the same time secure authentication.
With cidaas, you also have the option of establishing a fine-grained authorization concept that gives users access to specific functions or data depending on their authorizations. This is especially important in the connected home, where there are various devices with different access rights.
With functions such as Multi-Factor-Authentication, security can also be increased, for example when adding or removing devices in the connected home. As a Smart MFA – the multifactor can be used risk-based to enhance the security of the networked environment while improving the user experience.
With functions such as Multifactor Authentication, security can also be increased, for example when adding or removing devices in the connected home. As a Smart MFA – the multifactor can be used risk-based to enhance the security of the networked environment while improving the user experience.
Connected Home in a Nutshell
Connected Home promises to revolutionize the way we experience our homes. However, it also comes with challenges, especially in terms of the relationship between users and devices, as well as security. Solid authentication and authorization are key to ensuring that the connected home is not only convenient, but also safe and secure. The continued development of technologies in the field of security and privacy will allow us to fully enjoy the benefits of the connected home without compromising on security and privacy.
Would you like to learn more about the topic “Authentication and authorization of users on devices”? Then read our blog about this: Device authentication – it’s all about convenience!
