A unique approach for security at cidaas
Security and data protection are the keys
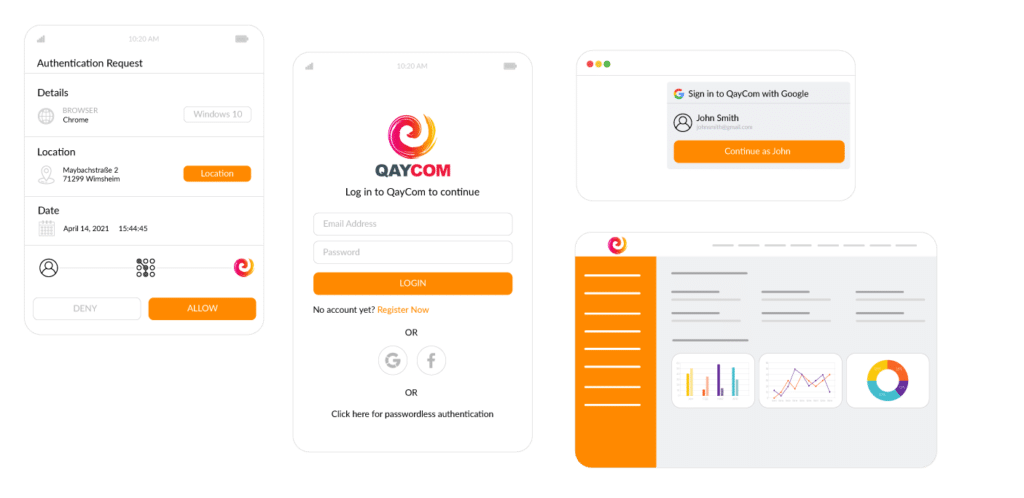
IT security and data protection are becoming essential criteria for modern digital services. Cyber threats and attacks are increasingly becoming a threat to the stable and secure operation of digital applications. Identity & Access Management plays a central role here, as it provides authentication and authorisation for users and is responsible for the administration of user data. It is not only the prevention of attacks on the Identity & Access Management service itself, as well as attempted attacks on the users, such as identity theft, but in particular also the functions provided by modern Identity & Access Management that ensure higher security. With cidaas, we offer comprehensive ways to integrate security into your digital applications, from multi-factor authentication to fraud and bot detection (more information in our feature set). Find out more on this page how we have integrated security into cidaas.
What we do for the security of our customers
Listed below are some of the most important measures that we have implanted in our DNA at cidaas:

The mindset at cidaas
While we considered a provider for infrastructure, all of our Security starts with the mindset. We know that security is important for our customers and users. Therefore, we at cidaas have established a unique mindset and awareness for the topic of safety. From the idea to development and operation, we live and breathe IT security.

We promote security awareness through targeted IT security awareness training.

We also integrate our partners into our measures and thus create a consistent understanding and awareness of IT security from product to integration.

Regular internal hackathons not only enable targeted penetration tests by cidaas, but also show colleagues what they work every day.

ISO9001 and ISO27001 certification at cidaas and the infrastructure partners.

We limit access to productive systems. All software and infrastructure updates are automated. And every access is monitored and logged.

The latest security measures in the infrastructure from firewalls to security information management.

Secure infrastructure
Security at cidaas starts at the very bottom level, the infrastructure. We select the right infrastructure partners with great care. We at cidaas as well as our infrastructure partners are ISO9001 and ISO27001 certified and meet the cidaas security and compliance guidelines.

Secure development with the cidaas Secure Development Lifecycle
At every stage of our development cycle, including design, coding, testing, and release, we place great emphasis on IT security. This way, we integrate security natively into the product instead of adding it afterwards. Our internal security team is directly involved in the development process.

We continuously train our architects, developers and testers in IT security, secure programming, and code reviews.

We have a software development process that follows a multi-level security and quality concept.

Software quality and vulnerability and IT security scans are directly integrated into our CI/CD pipelines.

Regular vulnerability scans analyse our code repositories.

Regular internal and external penetration tests and security audits.

Joint penetration tests with customers to validate integration in various applications.

Partnerships with research institutions and partners such as Fraunhofer for the development of IT security and penetration concepts.

Penetration and IT security testing
In addition to automated IT security tests and vulnerability scans, we rely on a combination of internal and external penetration tests. With our external partners and our customers, we manage to test cidaas including the integration into the applications. Each of our customers has the right to carry out penetration tests on their test environment.
Compliance

cidaas and the GDPR
The General Data Protection Regulation (GDPR) is one of the most important regulatory bases in Europe. As European Cloud Identity & Access Management, we live and breathe the GDPR, and we also work with partners on research projects relating to privacy-friendly platforms and business models:

We rely on European data centres and infrastructure partners – “Software Hosted in Europe”.

With commissioned data processing, you own the data, and we deliver the best service.

With the GDPR-compliant consent management from cidaas, you not only implement regulatory requirements, but also create transparency and strengthen the trust of your users.

With various certifications, we confirm our commitment and the compliance of cidaas.






